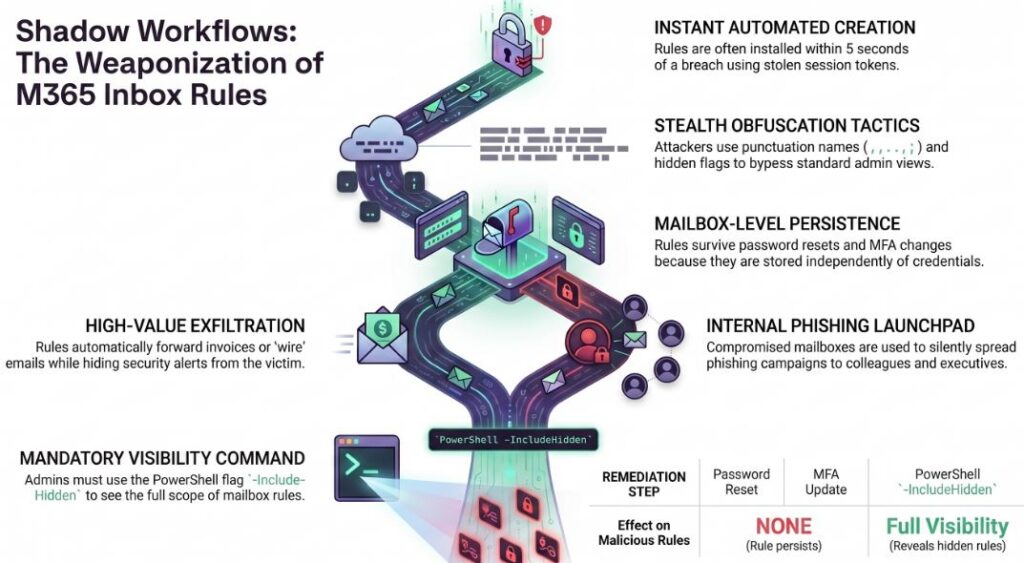
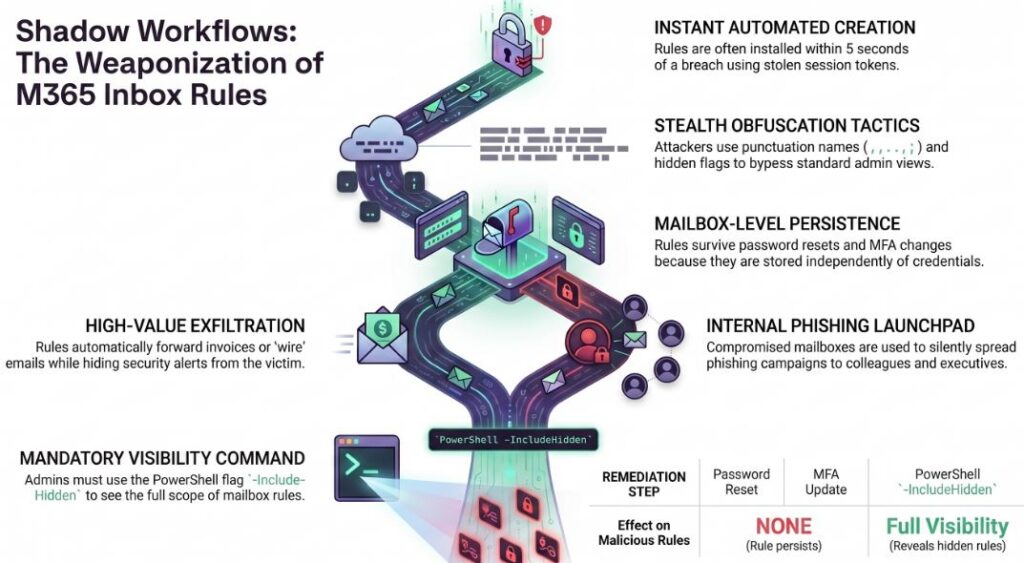
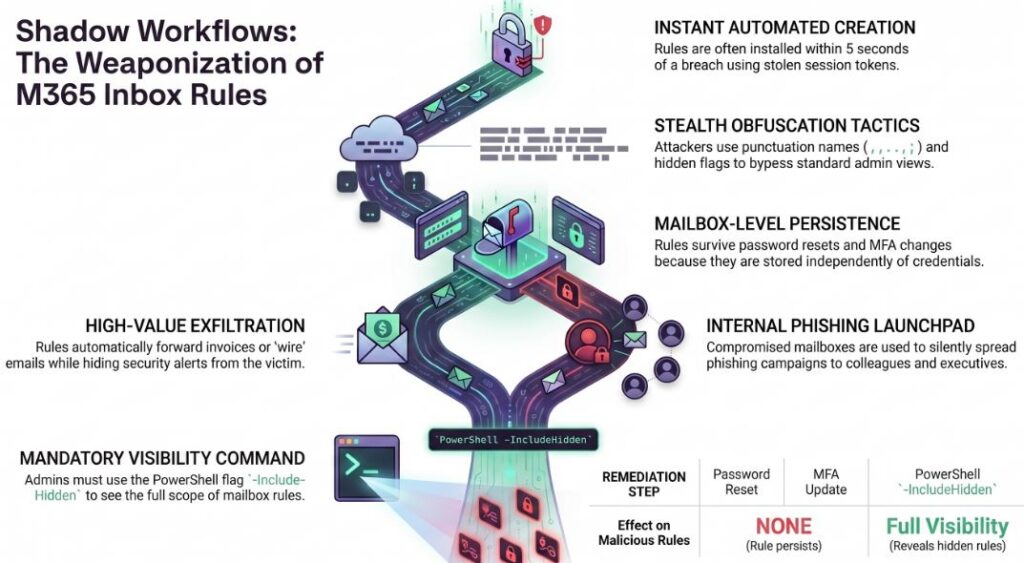
Microsoft’s INBOX Rules Hijacked by Hackers
Managed SOC as a Service with ProActive Attack Reduction

Summary: ABI tells you *what’s happening*. ACH tells you *why it’s happening*. One finds the mystery, the other solves the mystery. If intelligence frameworks were people, ABI and ACH would be the kind of couple you’d never seat next to each other at a dinner party. Activity-Based Intelligence (ABI) is the adventurous one always watching …
Read more “ABI vs. ACH: When Intelligence Analysis Feels Like Dating Two Very Different People”